
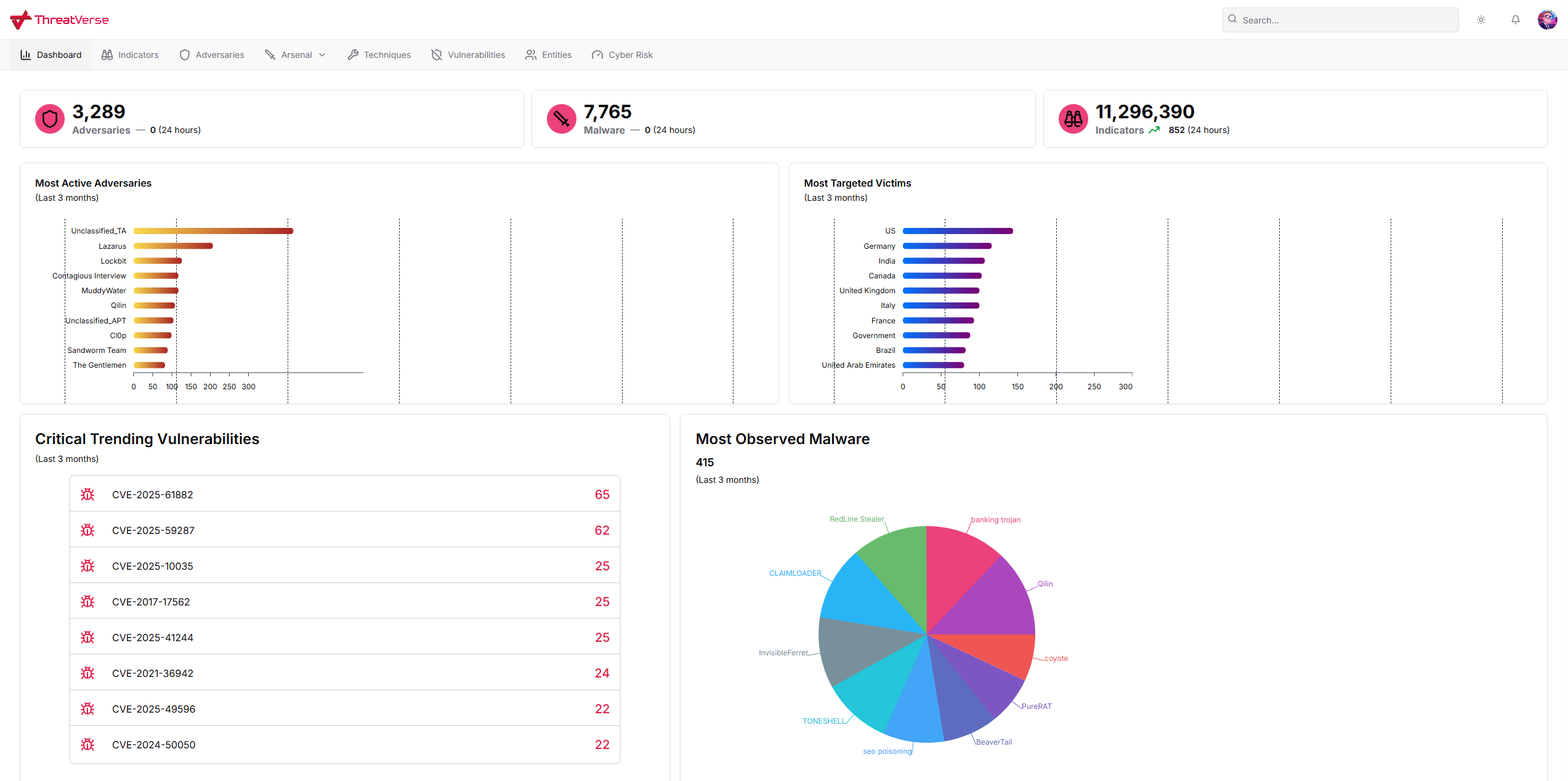
TIP: Aggregating intelligence from diverse channels—inclusing premium renown vendors as well as vetted open sources, empowering cybersecurity teams to defend against current threats and obtain a clearer forward-looking view of potential future risks.
ASM: Identifying and monitoring all exposed digital assets to proactively reduce vulnerabilities and strengthen security.

Compromises: deep and dark web monitoring service that detects compromised accounts and stolen cards being traded, enabling rapid action to protect users and reduce risk.
Vulnerabilities: Up to date infor of currently circulating CVEs.
As organizations increasingly rely on digital platforms and interconnected systems, they become prime targets for cybercriminals seeking financial gain, data theft, or disruption.
Cyber Risk refers to0 the potential threats and vulnerabilities that can compromise the confidentiality, integrity, and availability of systems and data.
Cyber risk can manifest across a variety of risk scenarios, each affecting organizations differently, depending on the nature of the threat and the assets involved.
Cyber deception strategically deploys realistic decoys, traps, and false assets throughout your network to lure adversaries away from real systems.
Every interaction is captured in real time, providing high-fidelity alerts and deep threat intelligence without the noise of traditional security tools.
Detect intrusions early, stop lateral movement, and expose hidden threats before they ever reach your critical infrastructure.
Orci varius natoque penatibus et magnis dis parturient montes, nascetur ridiculus mus. Ut finibus nisl mi, sed venenatis lectus into congue at semper tellus consectetur